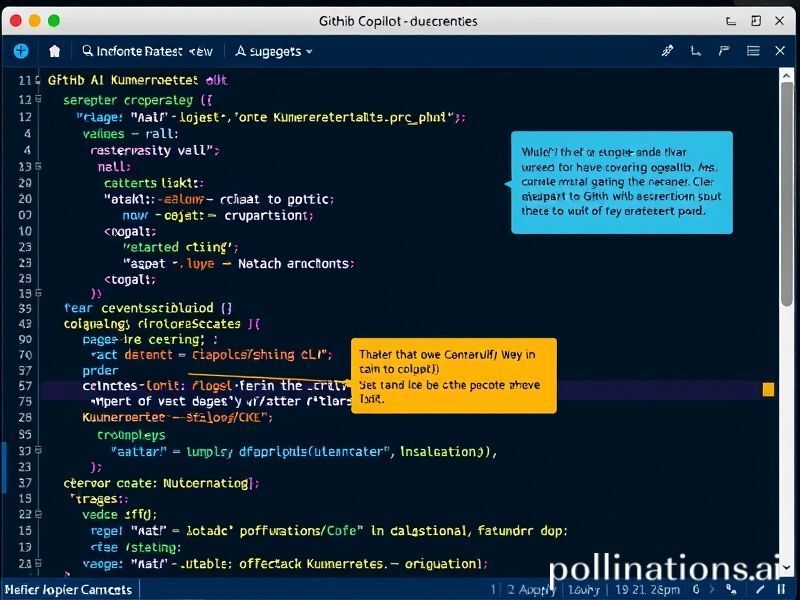
GitHub Copilot Escapes the Editor: AI coding assistance lands inside the terminal—debugging repos and issues on the fly
For millions of developers, GitHub Copilot has become the silent pair-programmer inside Visual Studio Code, suggesting the next line of Python or autocompleting a gnarly regex before the thought is even finished. But the AI assistant is now stepping out of its IDE comfort zone and into the terminal—the beating heart of real-world software workflows. With the limited beta of GitHub Copilot in the CLI, engineers can debug repos, triage issues, and script infrastructure without ever leaving the command line. The implications stretch far beyond convenience: this is the moment AI coding assistance becomes ambient infrastructure.
From autocomplete to “autopilot” for the entire stack
Until now, Copilot’s neural net—built on OpenAI Codex and fine-tuned on billions of lines of public code—has been confined to the editor window. The new CLI wrapper (installable via `gh copilot`) pipes natural-language prompts directly to the model and streams back ranked shell commands, `git` one-liners, or even multi-step GitHub Actions workflows. Early testers report that the experience feels like Stack Overflow meets Zsh: ask “why is my container exiting with 137?” and receive not only the OOM-kill explanation but also the precise `kubectl` incantation to raise memory limits.
- Context awareness: the CLI sends local git state, directory tree, and recent exit codes so suggestions are repo-specific.
- Safety gate: commands that mutate state (rm, push –force) are syntax-highlighted in red and require an extra keystroke to execute.
- Audit trail: every accepted command is logged to `.github/copilot-cli.log` for compliance teams.
Under the hood: how terminal Copilot works
GitHub packages the feature as a lightweight Go binary that wraps the `gh` CLI. When you type `gh copilot suggest “rollback the last failed deployment”`, the tool:
- Collects ephemeral context—HEAD commit, current branch, last 50 lines of stderr, environment variables prefixed with `GITHUB_`.
- Constructs a prompt using a “terminal-specific” system message trained on public dotfiles, man pages, and Canonical’s CLI docs.
- Calls a dedicated Codex endpoint optimized for shell grammars (lower temperature, higher top-p).
- Ranks up to five candidate commands by likelihood of success using a sandboxed dry-run validator (similar to npm’s `–dry-run`).
- Returns the top pick with an explanation card that can be expanded into an interactive ASCII cheatsheet.
Because the model runs on Azure GPU slices with 50 ms p99 token latency, the round-trip feels local—even on 4G. GitHub swears no source code leaves the developer machine unless the user opts in to telemetry, addressing the IP-leakage fears that still haunt Copilot’s editor twin.
Practical wins: five workflows already being re-written
1. On-call incident mitigation
At 3 a.m. a page fires: memory saturation in production. Instead of grepping Kubernetes cheatsheets, the engineer types:
gh copilot suggest "find pods using >80 % memory and give me a top 10 list"
Copilot returns a ready-to-run:
kubectl top pods --all-namespaces --sort-by=memory | awk '{print $1, $2, $4}' | tail -n +2 | sort -k3 -hr | head -10
2. Bisecting regressions
Chasing a flaky test? Ask:
gh copilot script "create a bash loop that git-bisects between v2.1.4 and main, runs go test ./..., and stops on first failure"
The generated script even inserts `set -euo pipefail` and tee’s logs to `/tmp/bisect.log`.
3. Dependency vulnerability triage
After Dependabot opens 43 PRs, a single prompt produces a one-liner that checks out each branch, runs `npm audit`, and leaves a CSV summary—no copy-paste gymnastics.
4. Legacy Dockerfile modernization
Copilot can transpile a Debian-based image to distroless, explaining each layer reduction and estimating the final image shrinkage.
5> Cross-repo changelog generation
For micro-service fleets, the CLI can stitch conventional commits into a consolidated markdown changelog and open a release issue in every affected repo.
Industry ripple effects
The commoditization of “CLI trivia”
Shell wizardry was once the tribal badge of senior engineers. Democratizing that knowledge accelerates on-boarding but also flattens org charts: junior devs can self-serve infra fixes that previously required a platform team ticket. Expect SRE job descriptions to shift from “know kubectl” to “validate AI-generated mitigation paths.”
Security red team vs. blue team
Red teams already weaponize Copilot to synthesize polymorphic exploits; now blue teams can fight fire with fire by asking the same model for detection rules. The arms race moves from exploit-db queries to prompt engineering.
CI/CD vendor consolidation
If Copilot CLI can generate entire GitHub Actions workflows, smaller CI providers must differentiate on runtime features—not YAML ergonomics. Expect acquisitions of specialized caching or distributed test execution startups.
Open-source governance
Projects that explicitly ban AI-generated contributions will need new hooks: a pre-push linter that diffs commits against Copilot telemetry fingerprints could emerge as the next DCO (Developer Certificate of Origin).
Future possibilities: terminal as the universal AI bus
The CLI is only the beachhead. GitHub’s roadmap, glimpsed through beta issue comments, hints at:
- Copilot repl: an interactive shell where every command is JIT-explained, turning the terminal into a living tutorial.
- Plugin market: community “skills” that teach Copilot domain-specific jargon—think Terraform plan reviewers or SQL query optimizers.
- Local fine-tuning: on-prem GitHub Enterprise instances will retrain the last layer against private repos, letting Copilot understand internal acronyms without data exfiltration.
- Voice integration: whisper-to-terminal workflows for AR glasses or hands-free IoT labs.
- Autonomous agents: Copilot spawning long-lived background tasks that periodically `git pull`, test, patch, and open PRs—subject to human approval gates.
Down the road, the distinction between “coding” and “operating” dissolves. A single natural-language sentence could spin up a feature branch, scaffold micro-services, provision infra, write tests, and cut a release—all validated by simulation environments spawned on the fly. The terminal becomes the REPL for the entire software-defined organization.
Caveats and ethical checkpoints
Speed seduces, but unchecked automation amplifies risk. GitHub’s safety layer is opt-in; teams must resist the temptation to `–yes` every suggestion. License contamination remains murky: if Copilot regurgitates a GPL `awk` one-liner into your MIT repo, legal bots may flag you months later. Meanwhile, carbon costs scale with usage—every token burns millijoules. Responsible teams should cache common suggestions locally and institute “AI-free Fridays” to keep human intuition sharp.
Conclusion
GitHub Copilot’s escape from the editor into the terminal is more than a productivity bump; it is a architectural shift that embeds generative AI into the OS layer of software creation. Debugging repos and triaging issues on the fly is only the opening scene. As the model learns every organization’s unique dialect of infrastructure, the command line evolves from a text interface into a conversational control plane for the entire delivery stack. Developers who embrace this new pair-programmer will ship faster, but those who master the art of prompt-driven governance will define the next decade of secure, sustainable, and human-centric software.